From its modest beginnings in a obscure corner of the net, it spread like wildfire. It started as just a trivial script, but soon it evolved into something horrifying. This toxic code, fueled by wicked intent, began to infect everything in its path.
Websites crumbled under its weight, presenting nonsensical gibberish and channeling users to dangerous sites. The once vibrant world of the internet was stealthily transformed into a online nightmare.
- Analysts scrambled to find a solution, but this code was like nothing they had ever seen before. It was constantly evolving, always one step ahead.
- Firewall systems proved useless against its cunning attacks.
- The world watched in horror as the internet, once a symbol of progress and connection, fell victim to this devastating code.
Is there any hope left for the internet? This is the question that haunts every digital citizen today.
Unveiling Dede4d: A Deep Dive into Malware's Evolution
Dede4d, a sophisticated piece of malware, has emerged as a growing threat in the cybersecurity landscape. This malicious code is constantly adapting, making it difficult to detect and neutralize. Analysts regularly observe Dede4d's activities to understand its capabilities and create effective countermeasures.
Security professionals are diligently investigating Dede4d's design, which is characterized by its dynamic nature. This trait allows Dede4d to incorporate new functions easily, enhancing its adaptability.
Understanding Dede4d's evolution is vital for protecting networks from its harmful effects. By proactively addressing this threat, we can bolster our defenses and reduce the risk of cyberattacks.
A Glimpse into Dede4d's Darkness
Dede4d, a program/tool/platform, often perceived as a harmless entity/construct/mechanism, can tragically become a weapon in the hands of evil-minded individuals/malicious actors/those with ill intentions. This disturbing reality/chilling truth/frightening prospect highlights the danger/peril/threat posed by technology when misused/exploited/abused. The innocence/simplicity/apparent harmlessness of Dede4d can be easily manipulated/quickly exploited/seamlessly twisted to inflict harm/damage/suffering upon innocent victims/vulnerable targets/unaware users. It's a stark reminder/warning/illustration that even the most benign/neutral/harmless-seeming creations can be corrupted/twisted/subverted for malicious purposes/wicked schemes/nefarious goals.
- Furthermore/Moreover/Additionally, Dede4d's sophistication/complexity/depth can make it difficult to detect/hard to trace/challenging to identify when used for illegal activities/criminal purposes/devious plots.
- Consequently/As a result/Therefore, it is crucial/essential/imperative to educate/raise awareness/promote understanding about the potential dangers/risks/threats associated with Dede4d and to develop safeguards/implement security measures/create protective protocols to mitigate its misuse/abuse/exploitation.
Warning: Dede4d is a Cybersecurity Nightmare
In the ever-evolving landscape of cyber threats, a new player has emerged, causing significant alarm among cybersecurity experts. Dede4d, a sophisticated and stealthy malware strain, has been rapidly spreading across networks, exploiting systems worldwide. This insidious threat is known for its ability to evade detection, making it an extremely critical threat to individuals, organizations, and even critical infrastructure.
- This modus operandi involves silently penetrating target systems through a variety of approaches, including network vulnerabilities, insecure configurations, and zero-day exploits.
- Once inside, Dede4d can stealing sensitive data such as usernames and passwords, credit card details, and confidential documents.
- Furthermore, Dede4d has the potential to launch further attacks by hijacking networks
The alarming growth of Dede4d highlights the urgent need for heightened cybersecurity awareness and preparedness. Individuals must take proactive steps to defend themselves from this evolving threat by implementing robust security measures, staying informed about the latest vulnerabilities, and training employees.
Decoding Dede4d: Strategies for Defense and Detection
Dede4d threat continues to pose a significant threat to organizations. To effectively combat this evolving danger, it's crucial to implement robust countermeasures. A multi-layered approach encompassing analysis tools, coupled with education programs for personnel, is essential. By analyzing Dede4d's signatures, security teams can implement targeted measures. Regular updates to software and platforms are paramount in mitigating the impact of Dede4d.
- Deploying advanced threat intelligence platforms can provide valuable insights into Dede4d's tactics, techniques, and procedures (TTPs).
- Isolation can limit the lateral movement of Dede4d within a network.
- Advanced Threat Protection (ATP) solutions can detect and respond to Dede4d's activity in real time.
Thriving in the Age of Dede4d: A Guide to Cybersecurity
In today's online landscape, staying secure is paramount. Dede4d, a new era of complex click here cyber threats, poses growing challenge to individuals and organizations alike. To survive yourself in this volatile environment, it's essential to understand the evolving threat landscape and implement robust cybersecurity practices.
- Firstly, assess your existing security posture. Identify your vulnerabilities and prioritize mitigation strategies.
- Utilize multi-factor authentication for all devices. This adds an extra layer of protection against unauthorized access.
- Keep your software and hardware to patch flaws.
- Remain aware of phishing attempts and other social engineering tactics. Verify the authenticity of emails and websites before providing any personal information
By implementing these best practices, you can enhance your cybersecurity posture and thrive the challenges of the Dede4d age.
 Emilio Estevez Then & Now!
Emilio Estevez Then & Now!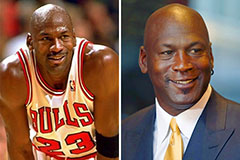 Michael Jordan Then & Now!
Michael Jordan Then & Now! Gia Lopez Then & Now!
Gia Lopez Then & Now! Soleil Moon Frye Then & Now!
Soleil Moon Frye Then & Now! Traci Lords Then & Now!
Traci Lords Then & Now!